Contents
Share this article
Key Takeaways
- Standard technical screening evaluates general engineering competence and leaves the fintech domain layer entirely unexamined.
- The five fintech domain knowledge gaps that most consistently cause production problems: monetary precision, payment idempotency, PCI DSS scope, KYC state machine design, and regulatory framework awareness.
- The most common red flag is a candidate who gives the right rule without demonstrating the mechanism behind it.
- Specificity in answers about failure modes correlates strongly with genuine production experience.
Most fintech hiring processes screen for the wrong things, which leads to developers working on systems they really don’t have the skills for, and mistakes that may not be identified until critical moments, like regulatory audits.
Vetting fintech developers requires five domain-specific screening areas beyond standard technical assessment:
- Monetary precision and data modelling (can they name why FLOAT is wrong?)
- Payment systems and idempotency (do they know the three-layer enforcement pattern?)
- Compliance architecture (can they scope PCI DSS correctly?)
- KYC/AML engineering (state machine vs. form?)
- Regulatory awareness (which frameworks apply to their role?).
Let’s go over how to vet fintech developers in a structured way, addressing each of the domain-specific screening areas mentioned. We’ll cover specific questions, what a genuinely experienced answer sounds like, and the red flags that reveal domain gaps before they become production problems.
At Trio, we do all of this screening for you, so you can access these fintech specialists in as little as 3-5 days, instead of spending weeks or even months trying to find the right person for your financial application.
Why Standard Technical Screening Isn't Enough
Standard technical screening, like coding challenges, system design interviews, and even behavioural questions, is a good starting point. They are more than enough to evaluate general engineering competence; however, the problem is that none of this evaluates fintech domain competence, because fintech domain competence doesn't surface in general software problems.
This means that you might miss fintech-specific knowledge or compliance gaps.
If these issues don’t show up in the pre-hiring vetting process, they inevitably show up when the developer starts writing fintech code. We often pick up on issues around 2–4 weeks in, when the first code review surfaces a data type error or a security review surfaces a PCI DSS scope problem that shouldn't exist. The cost at that point includes compliance review delays, architectural rework, and the timeline slippage.
And that’s if you catch the issue. If you miss it, you might run into issues during regulatory audits and might face massive fines as well as a loss in customer trust.
Screening Area 1: Monetary Data Modelling and Precision
Storing monetary amounts as floating-point numbers (FLOAT, DOUBLE) creates rounding errors that compound at transaction volume. A FLOAT representation of 0.1 + 0.2 doesn't equal 0.3 in IEEE 754 arithmetic.
This doesn’t really matter if you are only dealing with a handful of transactions, but if you scale to millions, as most banks do, then it produces a reconciliation gap that triggers a finance team investigation and potentially draws regulatory attention.
Our senior engineers who have worked on a variety of production fintechs cite this as one of the first things they check when reviewing financial code from engineers new to the domain.
The screening question: "What data type would you use to store a monetary amount in a database, and what would you use in a JSON API response? Why?"
What a genuinely experienced answer sounds like
For the database, you are going to want them to answer NUMERIC or DECIMAL with defined precision and scale, because these are fixed-precision types that don't introduce rounding errors.
Alternatively, store in integer minor units (cents for USD) and convert at the display layer.
For the API response, you want them to mention a string, not a float. This is because floating-point serialisation and deserialisation across different languages and frameworks can introduce precision loss at the boundary.
The candidate should be able to explain why.
Red flags to watch for:
- "I'd use DECIMAL because it's more accurate than FLOAT" indicates that the candidate knows the rule, but perhaps can't explain the mechanism.
- "I'd use DOUBLE because it has more precision than FLOAT" is a correct observation, but the wrong conclusion. DOUBLE has more precision but carries the same fundamental IEEE 754 limitation.
- "I'd use whatever the ORM defaults to" is one of the most common red flags we see in practice. ORMs typically default to floats for decimal columns unless explicitly overridden, and a developer who defers to the ORM on monetary precision has never had to fix a rounding discrepancy in production.
Follow-up questions you should ask here include, "Have you ever encountered a rounding error in a financial system? What caused it and how was it resolved?"
Engineers with genuine production experience give specific answers. Engineers who haven't built financial systems give theoretical responses about what they would do.
Screening Area 2: Payment Systems and Idempotency
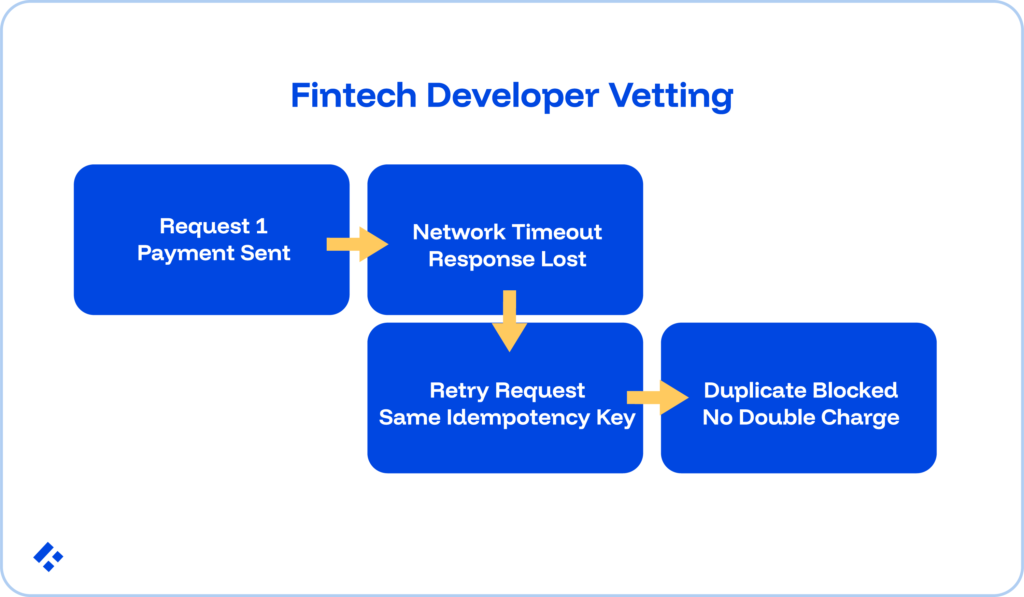
A user taps "Pay." The payment processes. The response gets lost in transit. The user taps "Pay" again.
Without idempotency enforcement, the payment processes twice, and the customer gets double-charged. This failure mode surfaces in production at every fintech that handles payments with engineers who understand idempotency but haven’t implemented it correctly.
It's the most common production incident in payment integration work by engineers new to the domain.
The screening question: "Walk me through how you'd implement idempotency for a payment endpoint. Where does the idempotency key come from, and how do you prevent a double charge if a network timeout occurs between the PSP confirming a charge and your database recording it?"
What a genuinely experienced answer sounds like
The idempotency key comes from the client, not the server. This means it is generated before the payment request fires.
If the server generates it and the response is lost, the client can't retry with the same key and has to generate a new one, which is what leads to a double payment.
The key applies at three layers:
- API gateway (request deduplication by key)
- Payment service (check for existing intent with that key before PSP submission)
- PSP (passed as a deduplication parameter so the provider won't charge twice for the same key).
It’s important that you probe your candidate to mention the write-ahead log gap.
This is where a window exists between the PSP confirming the charge and the database write completing. A production-grade solution uses a write-ahead record created before the PSP call, deleted only after the database write succeeds.
On recovery, unresolved write-ahead records trigger a PSP status query rather than a new charge attempt.
Red flags to watch for:
- "I'd use a UUID idempotency key" is an incomplete statement that doesn’t address where it comes from.
- No awareness of the write-ahead log gap suggests theoretical knowledge of idempotency without production-context experience.
- "I'd use the PSP's transaction ID as the idempotency key" is the answer, but backwards. The idempotency key must be sent to the PSP to deduplicate. Using the PSP's response ID means a second request gets a new ID and is processed again.
Follow-up questions you can ask here include, "What's the difference between a soft decline and a hard decline from a payment processor, and how does your retry strategy change for each?"
If your candidate really has fintech experience, they will be able to distinguish these immediately.
Soft declines (insufficient funds, temporary issuer unavailability) retry with back of, while hard declines (stolen card, account closed) never retry automatically.
Screening Area 3: PCI DSS Scope Awareness
PCI DSS scope determines the complexity and cost of security certification.
If your engineer doesn't understand the scope, they will make implementation choices that expand it unnecessarily by logging raw card data in debug statements, placing non-payment services in the same network segment as card data, and using shared credentials across systems that touch cardholder data.
The screening question: "If your application uses Stripe Elements or Adyen's hosted payment fields for card data collection, what is your PCI DSS scope and why?"
What a genuinely experienced answer sounds like
Hosted payment pages or JavaScript libraries (Stripe Elements, Adyen Web Drop-in) mean that your cardholder data travels directly from the browser to the PSP's servers.
Your application never touches the raw card data.
This lets you qualify for SAQ A, the lightest compliance path, because the application doesn't store, process, or transmit cardholder data directly.
You should also make sure that the candidate understands how using PSP tokens for all subsequent operations (capture, refund, recurring billing) maintains this minimal scope.
Red flags to watch for:
- "I'd need to implement full PCI DSS regardless" is incorrect and a significant knowledge gap.
- "PCI DSS doesn't apply to us if we use Stripe" is also wrong. Some requirements still apply (secure transmission, access controls), just far fewer than full scope.
- Confusion between SAQ A and SAQ D also matters, since SAQ D requires a full QSA engagement and security assessment while SAQ A is just a self-assessment questionnaire.
A good follow-up question here would be something like, "What would change about your PCI scope if you decided to store card tokens in your own database rather than in the PSP's vault?"
The domain-experienced answer is that PSP tokens have no value outside the PSP relationship and are not cardholder data, so storing them in your own database doesn't significantly expand PCI scope.
Screening Area 4: KYC/AML Engineering Design
KYC at a regulated fintech is not a form that calls a verification API and stores a verified boolean.
Instead, it's a stateful system with defined lifecycle states, regulated transition conditions, ongoing monitoring requirements, and EDD (Enhanced Due Diligence) triggers.
A developer who designs KYC as a simple verification form with a boolean flag produces a system that passes initial compliance review at low scale and fails under regulatory scrutiny as the customer base grows.
This is exactly the architectural failure behind the Monzo FCA fine (£21 million, July 2025).
The screening question: "Describe how you'd design the data model and state machine for KYC customer onboarding. What happens after a customer is initially verified?"
What a genuinely experienced answer sounds like
KYC needs a state machine, not a boolean. States should include at minimum: INITIATED, DOCUMENT_SUBMITTED, DOCUMENT_VERIFIED, LIVENESS_CHECK, SANCTIONS_SCREENING, RISK_SCORED, APPROVED, REJECTED, PENDING_EDD, SUSPENDED.
Your potential developer should understand that KYC is ongoing, not a one-time event. Initial verification is a state entry.
They also need to understand that a customer's risk classification can change based on transaction behaviour, and that change must trigger a state transition.
Red flags to watch for:
- "I'd add a kyc_verified boolean to the user table" is the most common red flag we see in this category. This design has no states, no transitions, no ongoing monitoring, and no EDD trigger.
- Treating KYC as complete at account opening is another major issue.
- Treating the KYC provider as "the KYC system" is also a frequent misunderstanding.
A good follow-up question here is, "What would cause a previously approved customer to re-enter a review state?"
Experienced answers are specific, while generic answers reveal theoretical rather than practical knowledge.
Screening Area 5: Regulatory Framework Awareness
A fintech engineer doesn't need regulatory knowledge at a compliance officer's depth, but they do need to know which frameworks apply to the systems they're building, what those frameworks require at the engineering level, and when to escalate a decision.
An engineer who builds a credit decisioning model without knowing ECOA requires adverse action notice capability, or builds an EU payment product without knowing DORA applies to their third-party API dependencies, creates compliance gaps.
What a genuinely experienced answer sounds like
- For a payment engineer: "What compliance frameworks apply to a payment system that processes card transactions and ACH transfers? What does each require from the engineering team specifically?" Expected answer covers PCI DSS (cardholder data security, same-day ACH windows, return codes, prenote requirements), and potentially FinCEN reporting for large transactions.
- For a backend engineer building consumer credit: "What engineering requirements does ECOA impose on a credit decisioning system?" The expected answer should be about how the system must be able to explain why an application was declined in specific, articulable terms.
- For a backend engineer at a UK or EU fintech: "What does DORA require of fintech companies regarding third-party technology providers?" Expected answer: classification of the technology supply chain by criticality, resilience testing of critical providers, and documented exit strategies.
Red flag to watch for:
A candidate who responds to engineering-level regulatory questions with "our compliance team handles that" isn't operating at the seniority level the role requires.
The Complete Vetting Framework
The five domain screening areas above complement standard technical assessment rather than replace it. A complete fintech developer vetting process covers both layers.
Standard technical assessment (necessary but not sufficient):
- Coding evaluation appropriate to the role: data structures, algorithms, language proficiency
- System design interview at the scale the role requires
- Code review of a recent project or take-home
- Reference check focused on production system quality and reliability
Fintech domain screening (what distinguishes fintech-competent from fintech-adjacent):
- Monetary precision: FLOAT vs. NUMERIC, API string representation, IEEE 754 explanation
- Idempotency: client-side key generation, three-layer enforcement, write-ahead log gap
- PCI DSS scope: hosted payment pages, SAQ A vs. SAQ D, token storage implications
- KYC state machine: states and transitions, ongoing monitoring requirement, EDD triggers, provider vs. state machine distinction
- Regulatory awareness: framework identification by role, engineering implications, escalation judgment
If you are reviewing a candidate and notice that they struggle in two or more of the five domain areas, we recommend that they be treated as a general engineer.
This means you are going to have to invest in significant fintech onboarding before working independently on compliance-sensitive systems.
Common Hiring Mistakes When Screening Fintech Developers
Mistake 1: Testing general coding ability and calling it fintech screening. LeetCode challenges test algorithmic thinking. Both matter for fintech roles, so you need to make sure that you are screening for both.
Mistake 2: Accepting "I've worked at a fintech company" as domain experience. A developer who built the marketing website for a fintech startup has not built payment systems.
Mistake 3: Asking regulatory questions that test memorisation rather than application. "What is PCI DSS?" tests awareness. "If I log the full card number in a debug statement during testing, what does that do to my PCI DSS scope?" tests the application.
Mistake 4: Not asking about failure modes. "What's the most common mistake you've seen in fintech payment integration code?" is one of the most revealing questions available. Engineers with production experience give specific, detailed answers.
Mistake 5: Treating compliance knowledge as optional for backend roles. Every backend engineer working on a fintech product touches compliance-sensitive systems eventually. Treating regulatory awareness as a nice-to-have for backend roles produces the architectural gaps that surface in compliance reviews.
Related Reading: Fintech Career Paths: Compliance, Jobs, and Roles
What "Pre-Vetted for Fintech" Actually Means
When a staffing partner claims to offer pre-vetted fintech developers, the claim only carries weight if the vetting covers the domain layers described above.
It is important that you make sure they are not just vetting for general engineering quality.
Here are three questions worth asking any staffing partner you are considering:
- "What specific fintech domain knowledge does your vetting assess?" A credible answer names the specific areas like monetary precision, idempotency, PCI DSS scope, KYC architecture, and regulatory framework awareness.
- "What is your acceptance rate for fintech developer applicants?" Rigorous fintech-specific vetting should produce a low acceptance rate. Published market data suggests acceptance rates of 10–20% for serious fintech-specific vetting processes.
- "How do you verify that a candidate's claimed fintech experience reflects genuine production exposure, not theoretical knowledge?" Look for: specific project references verified, specific technical decisions attributed to the candidate, or live technical screening against domain-specific questions.
Trio's vetting covers all of the domain areas we have already spoken about, and is supplemented by reference checks that verify production fintech experience specifically.
Developers are then hand-picked based on your specific requirements, so they are guaranteed to have all the right skills, leading to a 3-5 day placement time, with easy replacement guaranteed, further minimizing your risk.
Frequently Asked Questions
Engineers without fintech domain experience typically require 4–8 weeks to reach compliance-aware productive velocity on regulated fintech systems. During this period, they can contribute to general engineering tasks but should not work on compliance-sensitive components.
Yes, you should add fintech domain screening to your process for contractors and outsourced engineers, as well as for full-time hires, because contractors typically ramp faster and have less organisational oversight, catching domain mistakes early.
A fintech-competent developer applies domain conventions instinctively. They use NUMERIC, not FLOAT, for monetary amounts, generate idempotency keys client-side, scope PCI DSS correctly before writing integration code, and design KYC as a state machine with ongoing monitoring rather than a one-time verification flow. A general developer with claimed fintech experience often knows the regulatory frameworks by name without necessarily knowing their engineering implications.
To find out if a fintech developer has genuine production experience, ask about failure modes, not correct answers. “What’s the most common mistake you’ve seen in fintech payment integration code?” produces specific, detailed responses from engineers with production experience and generic answers from engineers with theoretical knowledge.
When hiring a fintech developer, you need to ask technical questions that go beyond general software engineering questions when hiring a fintech developer. Ask specifically about monetary data types, payment idempotency, PCI DSS scope, KYC architecture, and regulatory frameworks.

Expertise
- JavaScript
- NGX
- HTML
- Node.js
- Vue.js
Subscribe to our newsletter
Related
Content
Continue Reading