In fintech, security can unravel for a variety of different reasons. For example, a contractor might receive broad production access to move faster, or credentials may get shared in a private message to unblock a deploy.
Then, clients and regulators start asking about device policy, credential storage, and production access controls, and you are left scrambling.
An increase in developers using AI to code, providing these systems with access to a variety of data, is only adding additional complexity to security best practices.
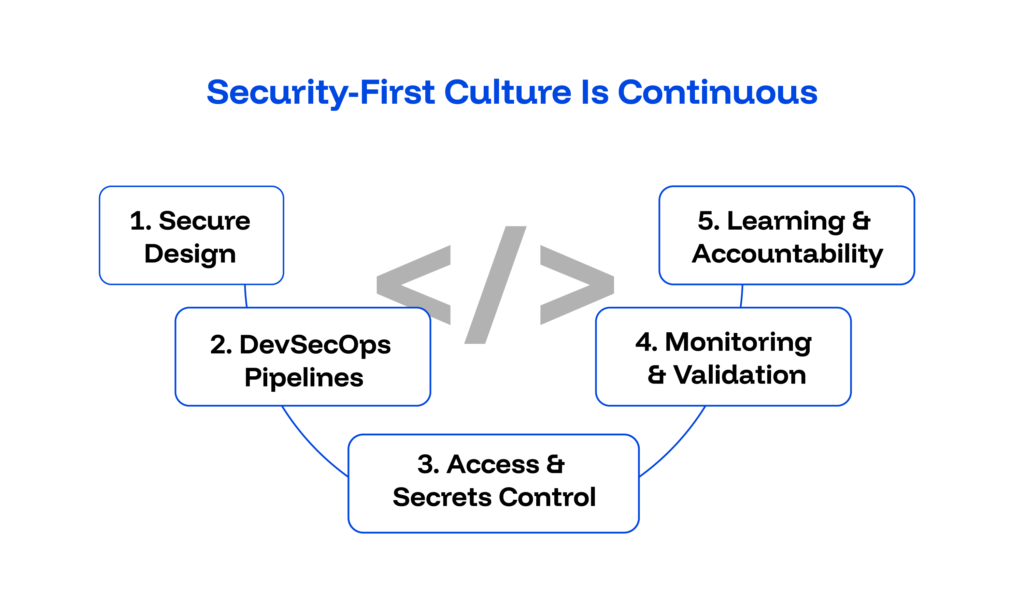
To build a security-first culture in fintech engineering teams, you need to design boundaries and enforce them early. You also need to document decisions before regulators or clients ask. That approach turns cybersecurity from a reactive cost center into a structural advantage.
When done well, it shapes a security-first organization where security is woven into architecture and workflow from day one. Our fintech experts place the utmost focus on security and compliance, and help our clients do the same.
Let’s look at the steps you need to take to ensure that you build a security-first culture in your fintech engineering teams.
Key Takeaways
- A strong security culture reduces audit friction because controls generate evidence automatically, and that evidence is stored in a way that is very easy to reach when you need it.
- Least privilege and environment separation shrink blast radius, especially when vendors and distributed teams contribute to production systems.
- DevSecOps strengthens delivery velocity by embedding security checks into pipelines so that you can avoid last-minute reviews.
- Leadership plays a critical role in security by formalizing risk acceptance decisions instead of letting each team have its own standards.
- Continuous monitoring and clear escalation pathways help organizations build resilient systems that can actually stand up to threats long-term.
1. Implement Security as a Primary Feature
When security shapes systems before the first line of code lands in production, you can avoid expensive redesigns, fines, and lawsuits.
Security-first fintech teams assume systems are guaranteed to face an attack eventually. That assumption changes architecture decisions.
- Threat modeling becomes part of feature planning.
- API design includes strong authentication and explicit authorization boundaries from the start, aligning with best practices in security solutions.
- Sensitive data flows receive encryption standards early rather than retrofitted later.
Defense in depth also begins here, as each layer is designed to carry protective controls.
This has additional consequences, like the fact that logging becomes tamper-evident by design.
When security adjustments are required, teams can move quickly because they don’t have to build from the ground up.
2. Make DevSecOps a Daily Engineering Habit
You can reduce friction and last-minute audit panic when security checks execute automatically inside your CI/CD pipeline.
In mature fintech environments, security tooling runs alongside unit tests. Static application security testing, dependency scanning, and dynamic analysis surface vulnerabilities during pull requests. Critical findings block merges until resolved.
This is even more important now that developers are using AI coding tools to try to get work out faster. Instead of assuming that the AI has created secure code, what it produces should be heavily scrutinized and go through all the same checks as if it were human-written.
Infrastructure as code undergoes automated misconfiguration scans before deployment. Security reviews integrate into normal code review workflows rather than sitting behind a separate approval gate.
DevSecOps works because security becomes continuous feedback, not a quarterly checkpoint. Engineers see issues immediately and fix them while the context still feels fresh.
3. Enforce Least Privilege and Strong Access Governance
When access aligns tightly with role requirements, you limit breach impact.
Least-privilege access should govern everyone on your team, and everyone who has anything to do with your product. That includes even the smallest vendor.
Production access requires documented approval, remains time-bound, and generates auditable logs.
Clear ownership around identity management prevents orphaned accounts and situations where you have shared credentials.
You should also make sure that you follow up on these. Regular access reviews confirm that permissions still match responsibilities.
From what we have seen, regulators often examine governance, and structured access control often tells them more about maturity than any policy document.
4. Centralize Secrets and Strengthen Key Management
The best way to reduce preventable exposure is to make sure credentials never appear in source code or chat threads.
You should put any sensitive data in managed vault systems with enforced rotation policies.
Encryption keys are pretty standard at the moment, but require secure lifecycle management, including controlled issuance and documented revocation.
Secure key handling often differentiates resilient fintech systems from fragile ones. A single exposed API key can undermine an otherwise strong architecture.
Centralization also simplifies compliance evidence because issuance and rotation history remain recorded automatically, supporting best practices in security management.
5. Build Continuous Learning Into Engineering Rituals
When engineers understand how real attacks unfold, repeated mistakes become highly avoidable.
Security awareness cannot rely on one onboarding session. Effective fintech teams host recurring secure coding workshops tied to real use cases such as payment processing, KYC workflows, and token-based authentication.
This is also where working with a fintech-specialist partner like Trio comes in. Our fintech engineers don’t just know the theory; they have been present for real-world issues, which gives them invaluable insight.
Internal briefings on emerging attack patterns are a great way to keep threat awareness current. Simulations and incident response exercises allow engineers to practice decision-making before a real event forces it.
6. Break Down Silos Between Engineering, Security, and Compliance
You prevent boundary failures when risk discussions happen across teams instead of in isolation.
We often see security breakdowns occur where ownership feels unclear. Strong fintech organizations create shared visibility into vulnerabilities and compliance status.
Engineering collaborates with security during design reviews. The product works with compliance when defining requirements. Operations participates in incident response planning and post-mortems.
This cross-functional alignment ensures that security decisions support business goals rather than compete with them.
7. Reinforce Secure Behavior With the Right Tooling
Secure development becomes easier than insecure shortcuts when tooling removes friction, promoting a culture where security is everyone’s responsibility.
Automated static and dynamic testing catch issues early, and runtime monitoring and anomaly detection surface suspicious behavior after deployment.
Even better, a custom, real-time dashboard can provide visibility into system health and risk posture.
When repetitive security checks run automatically, engineers focus on solving meaningful problems instead of manually validating the same controls.
8. Align Incentives With Security Outcomes
You sustain long-term discipline when performance metrics reward secure decisions, not just feature velocity.
High-maturity fintech teams recognize engineers who proactively improve security posture. Visible and invisible support, like remediation timelines and incident prevention efforts, should factor into performance discussions.
Similarly, if shipping speed remains the only metric that matters, security will quietly erode.
9. Move Beyond Annual Audits to Continuous Validation
It is a lot more effective when validation happens every week, not once a year.
Penetration tests and regulatory audits still matter, and those may be tied to an annual timeline, but modern fintech systems evolve incredibly fast.
Ongoing vulnerability monitoring is critical. An added benefit is that, when auditors arrive, evidence already exists because controls operate daily.
Why a Security-First Culture Matters More Than Ever
Fintech companies operate in an environment where cybersecurity failures carry immediate financial and reputational consequences.
When you deal with people’s money and sensitive personal information, a single breach can trigger regulatory scrutiny and cause you to lose the trust of both your clients and business partners.
The problem is that the industry is far from stagnant.
Cyber threats continue to evolve. Cybercriminals increasingly rely on automation and AI-driven phishing campaigns that scale faster than manual defenses. Social engineering attacks target engineers and finance teams alike.
On top of all of that, developers now use code generated by tools like GitHub Copilot or similar platforms, which may not be entirely secure, or which may encourage improper credential handling or create vulnerabilities in other ways.
While you need to pay attention to the technological aspects, a culture of security must reinforce every layer of defense.
Regulators and enterprise clients aren’t just going to trust that you are getting things done correctly. They expect detailed answers about your organization’s security posture.
They want clarity on credential handling, environment separation, next steps, and audit logging. When those answers rely on verbal assurances instead of documented security controls, you not only portray yourself as unprofessional, but doubt also creeps in.
Vendor risk compounds the challenge. We often see new startups overlook this, only to suffer the consequences later.
Distributed engineering teams and integration partners all introduce potential exposure.
Without structured access governance and consistent cybersecurity practices, risk expands quietly across your whole organization.
Related Reading: Best Risk Management Software
Security-First Misconceptions
Many teams claim they build a security-first culture, but their processes tell a different story. We have seen some misconceptions surface continuously over time.
Security Isn’t a Final Checklist
Security isn’t a phase at the end of a sprint, and when teams treat security checks as a final gate before release, they create expensive rework cycles.
A lot of teams also just can’t afford the security expertise early on, but when architecture decisions are made without security input, they often require retroactive fixes that slow delivery and frustrate engineers.
Good Intentions Without Operational Controls
Valuing the security conceptually does not produce strong security.
Talking about building securely is one thing, but without documented access policies and the processes in place to enforce that documentation, a security culture is just a pipedream.
To figure out if this is you, ask key questions. Who approves production access? How do credentials rotate? Where do logs aggregate?
If those answers depend on informal conversations, your organization’s security lacks structural depth.
Speed Versus Security Is a False Tradeoff
A lot of the teams that we work with assume that strong security inevitably slows product velocity.
In reality, unclear security boundaries create more delays than defined ones. Audits are notorious for causing these issues as they trigger emergency remediation efforts that disrupt roadmaps.
How Trio Embeds Security into Fintech Engineering Teams
You reduce vendor risk when your engineering partner aligns with your security expectations from the start.
At Trio, fostering a security-first culture begins before a single line of code ships. Our fintech engineering experts have worked on countless projects in a variety of regions, from Paytech and neobanking to Insurance platforms and more.
On top of that, there are some additional measures we take to ensure the utmost security.
Structured Security Onboarding
Every Trio engineer enters through a defined onboarding process that emphasizes NDA and IP protection, and a variety of other security standards.
On top of that, we make sure that our engineers have the time and resources for additional cybersecurity training aligned with fintech realities.
Least Privilege and Environment Separation
Trio teams follow least privilege principles by default. Access requests move through documented approval workflows, and production access remains restricted and time-bound.
Environmental separation between the different stages of development also prevents accidental data exposure. Logging and monitoring reinforce those boundaries and support audit readiness.
Transparent Incident Escalation Pathways
When potential security incidents arise, clear escalation pathways guide response. Our teams are all familiar with what needs to be done ahead of time and work alongside client security teams to make sure these next steps are taken quickly.
That structured coordination strengthens the overall security posture and demonstrates shared responsibility in action.
Conclusion:
In short, you build a security-first culture in fintech by embedding controls into architecture, implementing measures like access restriction, and more.
Creating a security-first culture is not a one-time job, but a way of thinking that needs constant reinforcement across teams. When security becomes part of organizational culture and technical design, organizations withstand cyber threats without sacrificing innovation.
In fintech, trust determines longevity. A strong security culture protects data and maintains the trust of both regulators and clients.
Want to talk to Trio’s experts? Schedule a security-ready consult.
FAQS
What does it mean to build a security-first culture in fintech?
Building a security-first culture in fintech means embedding cybersecurity controls and access governance into daily engineering and leadership processes.
How can fintech companies integrate security into DevOps?
Integrating security into DevOps requires adding automated security checks, dependency scanning, access controls, information encryption, key handling, and more directly into CI/CD pipelines.
Why is least privilege important in financial services?
Least privilege in financial services limits access to sensitive systems. Every person or entity only gets the bare minimum to do what they need to, reducing blast radius if credentials are compromised.
How often should cybersecurity training happen in fintech teams?
Cybersecurity training in fintech teams should occur regularly. Since threats to the industry evolve all the time, it’s important to update teams on current threats and practice addressing those threats through techniques like simulations.
How can fintech startups prepare for security audits?
Fintech startups can prepare for security audits by documenting access controls, enforcing environment separation, and maintaining centralized logging.
What is DevSecOps in a fintech environment?
DevSecOps in a fintech environment integrates security testing and compliance checks directly into the software development lifecycle. In most cases, it aims to automate as much as possible.
How do you prevent security breaches in fintech companies?
Preventing security breaches in fintech companies involves least privilege access, continuous monitoring, structured incident response, and ongoing employee training. It is important to adapt to industry best practices, though, as fintech and its threats evolve quickly.






