Contents
Share this article
Developing quickly is one of the most effective ways to gain a competitive edge in fintech. If your development process takes months, your competitors are more likely to release something faster, decreasing the chances of your success.
However, fintech companies cannot simply focus on speed. Security practices are crucial when handling sensitive information. A single vulnerability in a payment API or a misconfigured cloud instance can lead to everything from regulatory fines to reputational damage. Ultimately, you’ll lose customer trust and revenue.
So, how do you balance application security and speedy software delivery at the same time? Enter: DevSecOps.
DevSecOps in fintech involves embedding robust security measures into every part of the development lifecycle, ensuring that, by the time you are ready for deployment, you haven’t missed anything.
At Trio, we’ve seen firsthand how companies that prioritize security and regulatory compliance can push ahead.
Our fintech-savvy engineering talent has worked on a variety of projects, helping companies establish everything from fundamental security automation to comprehensive incident response plans, all tested through threat modeling.
If you need to automate compliance and security, we might have the right people for you.
Schedule a security-ready consult.
Key Takeaways
- DevSecOps embeds security into every stage of the CI/CD pipeline, which tends to cut both the cost and the delay of remediating vulnerabilities in fintech systems.
- The financial services sector faces the highest average cost per data breach at $5.9 million, according to IBM's 2024 report, making proactive security automation a financial decision as much as a technical one.
- Frameworks like PCI DSS, PSD2, GDPR, and SOC 2 create compliance requirements that cannot realistically be met through manual review at release cadence. Automation is the only practical path at scale.
- Legacy core banking systems and monolithic codebases require additional middleware and API wrapper work before modern security automation can be applied.
What is DevSecOps in Fintech?
Before implementing DevSecOps in fintech, it’s essential to ensure you understand what it is and how it differs from traditional security approaches.
In short, DevSecOps is similar to DevOps, a set of practices that aim to break down the barriers between software development and IT operations, increasing speed and efficiency, while incorporating additional security practices.
You take the final product and all requirements into account at every stage, utilizing tools such as automated checks in your CI/CD pipeline (continuous integration, continuous delivery).
How DevSecOps differs from traditional security in financial services
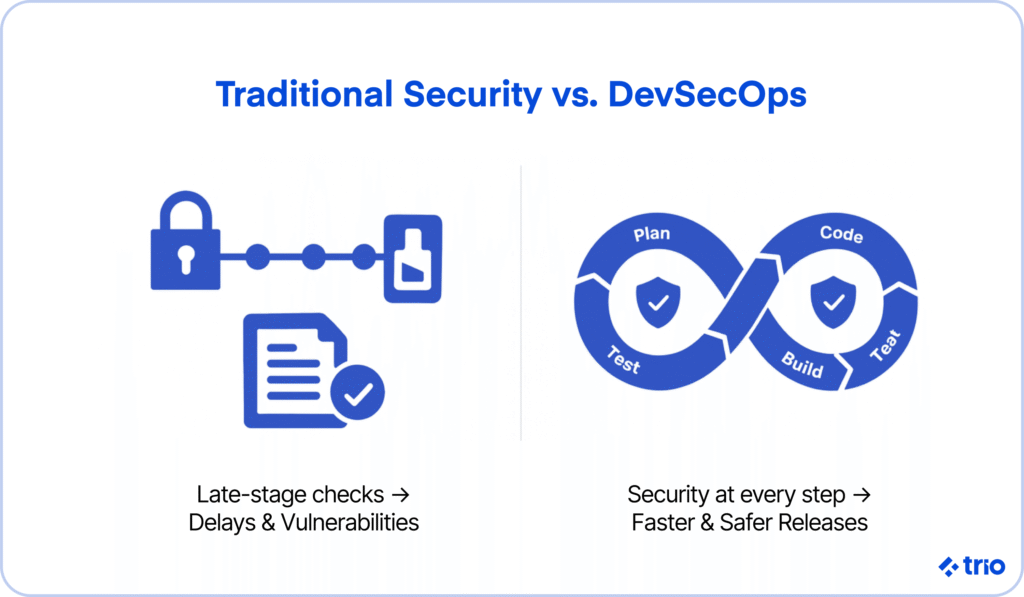
When it comes to more conventional app security, it’s almost seen as the last step. A quality assurance developer or security team will run a couple of final checks before you deploy your app to catch any vulnerabilities.
This approach can be considered outdated and fails miserably in the context of financial software development.
Regulatory bodies continually assess fintech applications to ensure compliance with frameworks such as PCI DSS, PSD2, GDPR, and SOC 2. If you make a mistake, these institutions could fine you heavily. Ensuring that everything meets their needs can also be quite expensive if done retroactively.
Then, as we mentioned above, speed-to-market pressure can be intense, as competition among different fintech organizations is fierce. If you discover any vulnerabilities just before launching your app, you can significantly delay potential releases, which may mean all your efforts have been in vain.
Through DevSecOps, which encourages both secure and efficient development, you consider security risks from the start.
The process involves integrating security checks, compliance requirements, and threat detection throughout your development pipelines, so that by the time you are done coding, you know everything else is ready to go.
Why fintech products have unique security and compliance demands
If DevSecOps practices are the most time- and cost-effective way to address security vulnerabilities, why doesn’t everyone adopt this practice approach?
Security isn’t as essential in apps like simple mobile games. Competition may also not be as great.
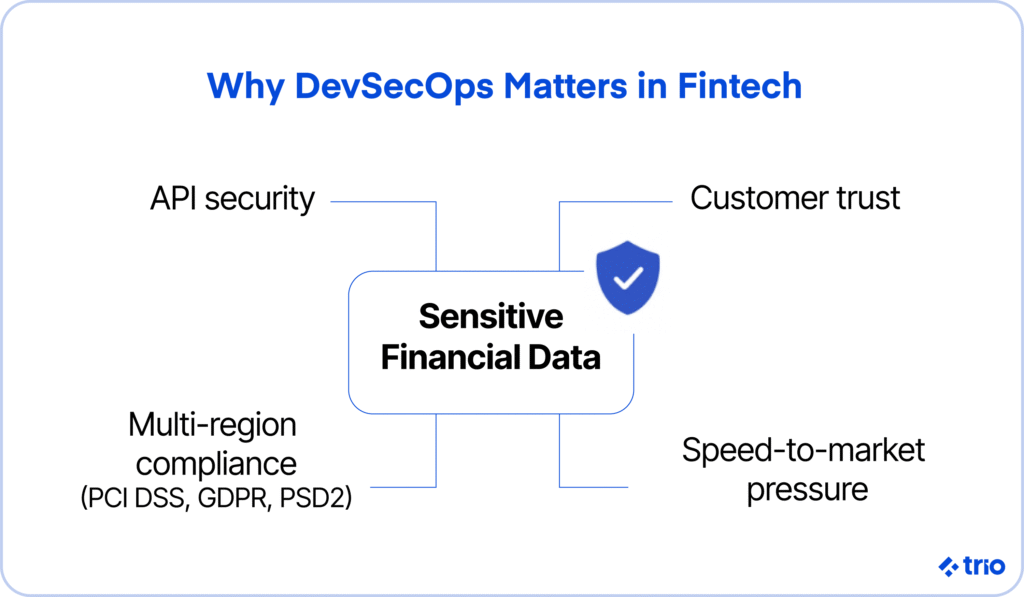
Fintech deals with sensitive financial data, integrates high-value APIs, and sometimes operates over more than one regulatory jurisdiction. Even small choices mean that people may lose their trust in you. Ensuring security and compliance is non-negotiable.
Why DevSecOps Matters for Financial Services Leaders
As we have already briefly mentioned, DevSecOps represents more than just getting your security early. It represents the opportunity to build faster and safer, opening up opportunities for innovation.
The rising cost of security gaps in production
According to IBM’s 2024 Cost of a Data Breach Report, the financial services sector faced the highest cost of a cyberattack at $5.9 million per breach.
We believe the actual number is likely far greater when considering the additional losses incurred when customers lose trust in your services.
In some cases, these breaches may start small enough that your clients may not even know about them, and your developers may only pick up on the issues later. Some common examples we’ve seen include a misconfigured S3 bucket, an outdated open-source dependency, a missing API authentication check, and so on.
How security impacts speed-to-market and customer trust
Since security is so critical in financial technology, and most industry regulations insist on it, vulnerabilities act as a hard stop. However, even if you ignore this, there are other reasons why you want your teams to focus on security early.
It may seem like including proactive security in the entire software development lifecycle (SDLC) takes longer, but it is the fastest option. You can set up automated checks, which are not only faster but also catch issues earlier, preventing the need to rework large sections of code.
And, when customers know that you take security seriously, it can be a boost to your brand image, setting you apart from competitors with similar products.
Regulatory consequences of insecure development
Of course, fines are expensive. In recent years, we have seen that regulatory bodies, such as the GDPR, aren’t afraid to impose penalties, even targeting global tech giants like Google. The company was fined around €50 by the French National Commission on Informatics and Liberty (CNIL) in 2019.
In addition to the substantial monetary fines you will incur, consequences such as having your license revoked under PSD2 and failing security audits may even compel you to cease offering your products in certain jurisdictions.
DevSecOps solutions alleviate this stress by ensuring continuous compliance evidence through automation, thereby relieving pressure from your team and providing shareholders and non-technical leadership with evidence of your efforts.
Related Reading: Tokenization as a Service: Data Security
Challenges of Embedding Security into Fintech CI/CD Pipelines
Moving towards DevSecOps offers a variety of benefits, but implementing built-in security mechanisms in a field that shifts as quickly as fintech can be challenging.
Fragmented security toolchains and workflows
It is common for fintech teams to work with a range of security scanning tools, manual checks, and spreadsheet-based compliance tracking systems.
Fragmentation like this can often lead to slowed development. It can leave blind spots or even create confusion.
If you are using developers new to the industry, they may not be familiar with all the tools either, and the variety means that the amount of time required to learn everything will be pretty extensive. The same can be said for any onboarding of new hires.
Fintech code review automation is the best way that we have found to address part of this problem.
When code review tools integrate natively into the CI/CD pipeline and flag security issues as part of the normal pull request process, developers encounter feedback in context rather than as a separate audit step, which tends to produce faster remediation and less resistance.
Developer resistance to friction-heavy checks
If you have separate teams for development and security monitoring, there may be a difference in priorities. Your security teams may introduce tools that serve their purposes well, but which add build delays or require a lot of manual effort.
Developers could push back because these steps decrease their productivity, hindering delivery goals.
Legacy systems and technical debt are slowing automation.
Many fintech companies collaborate with traditional institutions, such as large banks. The problem is that these institutions have older core banking systems, payment gateways, and monolithic codebases that are incompatible with modern APIs and integration points.
In some cases, it is possible to make minor adjustments to make the legacy software more manageable. But, more often than not, you need to implement a variety of workarounds to enable things like automated security checks.
Working with legacy code is not impossible, but it does take additional time, effort, and industry knowledge.
Related Reading: Real-Time Fraud Detection and Prevention
The People and Process Layer of DevSecOps in Fintech
DevSecOps in fintech does not succeed on tooling alone. Teams need shared ways of working that treat security and compliance as part of daily delivery rather than a final approval step.
Building a strong DevSecOps culture means focusing on continuous improvement, cross-functional collaboration, and secure, repeatable delivery.
Fintech teams operate under constant pressure to ship quickly, but pushing volume over quality often leads to rework, delayed releases, or last-minute security findings. A security-by-default mindset reduces those risks by surfacing issues earlier and making secure patterns easier to follow.
A healthy engineering culture also encourages developers to raise concerns early, propose improvements, and ask for help when something looks wrong. In practice, this shifts security from a bottleneck into a shared responsibility across development, security, and operations, with customer trust as the common goal.
DevSecOps Operating Cadence for Secure, Fast Releases
Short, repeatable delivery cycles reduce both security risk and release friction. Working in sprints and testing for security, compliance, and scalability on a continuous basis allows teams to fix issues while changes remain small and easier to control.
DevSecOps builds security checks, threat modeling, and automated testing into the normal CI/CD workflow instead of leaving them for a separate phase. This approach catches vulnerabilities earlier and prevents late-stage surprises that can block a release entirely.
Smaller, more frequent releases also limit the impact of failures and make it easier to trace problems back to specific changes. In fintech environments, where a single missed control can delay or cancel a launch, this cadence usually delivers faster outcomes than large, infrequent deployments.
Security Ownership Models in DevSecOps Teams
DevSecOps shifts security from a single team’s responsibility to a shared ownership model across product and platform teams. Teams take responsibility for their own pipelines, services, and risk areas, while security specialists focus on building standards, shared tooling, and automated policies.
This model reduces handoffs and avoids last-minute approval bottlenecks. Practices such as incident reviews, service-level objectives, and real-time alerting, commonly used in Site Reliability Engineering, help teams balance delivery speed with operational risk.
The result tends to show up in fewer production surprises, clearer accountability, and better visibility into how everyday engineering decisions affect security and compliance.
Platform Teams and CI/CD Guardrails for Secure Autonomy
As fintech organizations scale, security controls need to become repeatable and easy to consume. Internal platforms and shared services make this possible by providing secure-by-default CI/CD pipelines, approved infrastructure templates, and policy-as-code guardrails.
Infrastructure as Code helps teams create consistent environments and reduces configuration drift, while automation cuts down on manual errors and review overhead. Developer portals and self-service workflows further remove friction, letting teams ship faster without bypassing controls.
This structure keeps standards centralized while allowing product teams to move quickly within safe boundaries, which improves both delivery speed and auditability.
Cloud identity and access management play a critical role here.
In fintech release pipelines, integrating identity providers with your CI/CD toolchain, so that every deployment action carries an auditable identity rather than a shared service account, sets you up for audit success.
Hiring Fintech DevSecOps Engineers for Compliance and Scale
One of the most expensive mistakes fintech companies make involves hiring engineers without experience in regulated environments. Domain expertise matters when systems must meet strict security, compliance, and reliability requirements.
Engineers who have worked with financial data, payment systems, and compliance-driven pipelines make better architectural decisions early and reduce the need for costly rework later. That experience shortens delivery timelines and lowers operational risk as systems scale.
At Trio, we provide fintech-specialist engineers familiar with the U.S. regulatory environment, while keeping costs competitive through talent from LATAM and Africa. This gives companies access to DevSecOps-ready teams that can move faster without compromising on security or compliance.
DevSecOps Best Practices for Fintech Development Teams
Expert DevSecOps developers in the fintech sector implement best practices to ensure success, even when working on the most complex fintech projects. These include:
- Shift-left security testing from the design stage: Where early threat modeling helps identify potential vulnerabilities.
- Role-based access control and secrets management: Each role has limited permissions, and automated secrets rotation prevents credential leaks.
- Using secure coding patterns and frameworks built for fintech: Only fintech vetted libraries, which are guaranteed to meet compliance requirements, are used.
Automating Security in CI/CD Pipelines for Fintech
Many DevSecOps services rely on automation. Manual reviews and spot checks have their place, but they are impossible to maintain at any scale. Automating tests enables fintech companies to identify security incidents almost instantly, allowing them to scale rapidly without worrying about falling behind.
Continuous static and dynamic code scanning is a key component in transitioning your security from a reactive model to a proactive one. SAST tools (Static Application Security Testing) scan code before it’s compiled. DAST tools (Dynamic Application Security Testing) simulate real-world attacks against your apps.
If you automate both in your continuous integration and continuous delivery pipelines, you can identify vulnerabilities at various stages, enabling continuous improvement.
Secrets management and automated credential rotation are other standard automations that we often help clients with. Our developers help companies build automated secrets management systems, enabling them to store information securely and rotate credentials automatically without manual coding.
This technique is beneficial in many industries, but particularly crucial in fintech software development.
The automation we often overlook is likely automated third-party API dependency checks.
Fintech apps often utilize third-party payment processors, banking APIs, and other external services to minimize the amount of work they must do upfront. While this is the most cost-effective way to get started in the finance industry, you must ensure that you aren’t exposing yourself to additional vulnerabilities.
Securing payment workflows in fintech startups often begins here, with automated dependency scanning on the integrations that touch payment data.
Our developers can help you create dependency management tools that automatically scan these integrations for potential issues, allowing you to pick up real-time changes before any weaknesses can be exploited.
5 Steps to Build a Fintech-Ready DevSecOps Roadmap
To ensure that you are emphasizing a secure software development lifecycle (SSDLC) in your fintech application, you can split your DevSecOps into five different steps:
- Prioritize high-risk areas first: Focus on systems that handle sensitive financial data, customer authentication, and payment flows. Then you can move on to the other regions.
- Select fintech-savvy engineering talent: Fintech presents some unique challenges, especially when it comes to information security. Hiring developers who are familiar with the industry, such as those we provide at Trio, decreases the likelihood of costly mistakes.
- Automate what slows developers the most: It’s relatively simple to automate repetitive tasks. Having AI and ML handle the work for you eliminates the possibility of human error and enables developers to focus on other tasks.
- Measure with security-specific KPIs: Remediation time, number of automated tests, and compliance readiness scores are all great KPIs to track, as these give you a good idea of both speed and security.
- Foster a culture of continuous security improvement: DevSecOps is essentially a mindset of collaboration across your development, security, and operations teams. Encouraging a DevSecOps culture results in everyone recognizing their responsibility in protecting consumer trust and taking the necessary steps to achieve good results.
If you want developers who have worked through a fintech company’s DevSecOps journey before, you are in the right place.
Final Thoughts
At Trio, our developers are all fintech-savvy experts who spend their days helping companies in the industry with everything from basic security automation to complex integrations. When hiring through outsourcing or staff augmentation models, you get all of the benefits of these experts without the commitment of an in-house developer.
Our solutions are all custom-tailored to your requirements, ensuring you get precisely what you need. We have even helped companies establish dedicated teams of developers to help them achieve their goals.
If you’d like to learn more about bringing these industry experts onto your team, or you’re ready to start hiring, talk to an expert.
FAQ
What is DevSecOps in fintech?
DevSecOps in fintech is the process of embedding security into every part of the software development lifecycle. It ensures that you deal with vulnerabilities before they can be exploited and guarantees regulatory compliance.
How does DevSecOps help with compliance in financial services?
DevSecOps helps with compliance in financial services by ensuring that compliance requirements are integrated into your code, your audits are automated, and any changes in regulations can be easily taken into account.
Can DevSecOps work with legacy financial systems?
Yes, DevSecOps can work with legacy financial systems, but you may need additional software, such as middleware and API wrappers, or you may need to modify the legacy code to modernize it sufficiently for integration with security automation.
How does DevSecOps improve investor confidence?
DevSecOps enhances investor confidence by providing more information on how you are managing security risks and offering measurable KPIs for both security and scalability.
What makes a good CI/CD solution for fintech applications?
A CI/CD solution that is good for fintech applications requires integrated SAST and DAST scanning at each pipeline stage, secrets management that prevents credentials from appearing in build logs, role-based access controls with auditable identity at the pipeline level, and automated compliance checks against the frameworks your product operates under.
How do you secure payment workflows in fintech startups?
Securing payment workflows in fintech startups begins with mapping every point where payment data enters, moves through, or leaves your system, then applying controls at each boundary rather than only at the application layer.
Frequently Asked Questions

Expertise
- JavaScript
- NGX
- HTML
- Node.js
- Vue.js
Subscribe to our newsletter
Related
Content
Continue Reading




