Essential Mobile App Security Best Practices Every Developer Should Know
Contents
Share this article
With mobile apps serving as gateways to personal data, financial transactions, and user interactions, protecting apps from potential security threats is crucial for both developers and users.
For developers, taking proactive measures to ensure app security is essential in maintaining user trust and preventing data breaches.
If you are interested in rapid mobile app development through outsourcing or want to augment your staff by adding someone to your team for a longer period of time, reach out to us here at Trio.
We focus on retaining top developer talent who are familiar with the latest security protocols on iOS and Android devices, and their effective client communication has allowed us to build trust in software partnerships time and time again.
Let's look at the best practices that every mobile app developer should implement to create secure, reliable apps that stand the test of time.

What are the Key Mobile App Security Best Practices?
Mobile apps are susceptible to numerous security threats, from data breaches to malware attacks. Implementing best practices at every stage of development helps protect your app from these threats.
Understanding Mobile Application Security
Mobile application security focuses on safeguarding sensitive data, preventing unauthorized access, and ensuring the app's resilience against cyber threats.
This first security layer starts with strong encryption.
Implementing encryption for data at rest and in transit (also known as transport layer security is a non-negotiable best practice.
Advanced Encryption Standard (AES) with 256-bit keys is commonly used to protect sensitive information like passwords and payment details, ensuring that intercepted data remains unreadable to attackers.
This secure mobile app development becomes particularly important when you are working in fields like financial technology services, or Fintech.
Importance of Mobile App Security for Developers
Security for mobile devices and apps is critical for several different reasons.
A single security breach can have devastating consequences, including loss of customer trust, legal penalties, and financial losses.
By implementing strong mobile security measures, developers not only protect user data but also comply with regulations such as GDPR and CCPA, avoiding potential legal consequences.
At Trio, we have developers from all over the world, from Latin America to Africa and even Eastern Europe, who may make great additions to your team by providing knowledge on regulations and the different security solutions required.
10 Tips to Ensure Mobile Application Security
If you're a mobile app developer or are considering hiring one with the sole purpose of developing robust security measures, here are some of the top tips from Trio to ensure you are abiding by mobile application security best practices.
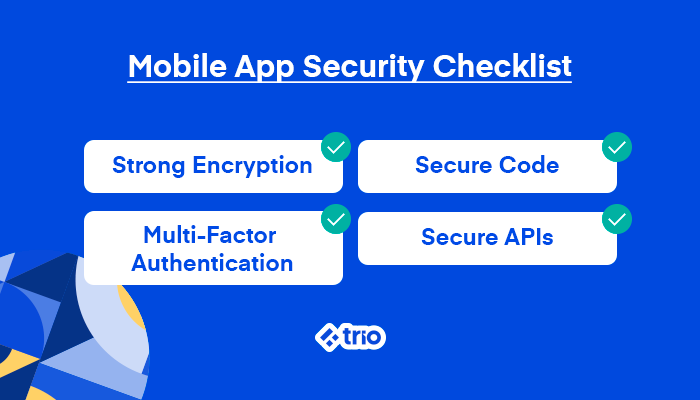
- Use Strong Encryption: Encrypt sensitive data both at rest and in transit to prevent unauthorized access.
- Secure Code Development: Write code with security in mind to avoid vulnerabilities like SQL injection and cross-site scripting (XSS).
- Authentication and Authorization: Use multi-factor authentication (MFA) for added protection, ensuring that only authorized users can access the app.
- Use Secure APIs: Protect API calls with secure tokens and enforce strong authentication to avoid data exposure.
- Implement SSL/TLS: Use secure communication protocols to encrypt data exchanges between the app and the backend server.
- Secure the Backend: Protect backend infrastructure with firewalls, intrusion detection systems (IDS), and frequent software updates.
- Data Minimization: Only collect and store the data necessary for app functionality, reducing the impact of potential data breaches.
- Monitor User Behavior: Detect suspicious activity early by tracking user behavior for any anomalies.
- Use App Sandboxing: Isolate app processes and data to prevent malware from affecting the rest of the device.
- Regular Security Audits and Pen Testing: Conduct frequent security audits and penetration tests to identify vulnerabilities.
How to Implement Secure Coding Practices in Your Mobile App?
It is essential that you adopt secure coding practices from the start to avoid introducing vulnerabilities that attackers can exploit.
Secure Code Development Techniques
We recommend that you start with input validation when developing secure mobile applications, ensuring that the app processes only properly formatted data.
Malicious inputs are one of the most common attack vectors, and proper validation and security checks can block potential exploits.
Use output encoding to prevent injection attacks such as cross-site scripting (XSS), where malicious scripts are injected into the mobile phone app to steal data or compromise the user's session.
Of course, secure code development is an ongoing process, so also ensure that your developers are always up to date on the latest iOS and Android development.
You should also ensure that your code is written in such a way that you can easily integrate an extra layer of security later. React Native's containerization is particularly great for this.
Common Security Vulnerabilities in Mobile Applications
Common security vulnerabilities include insecure data storage, improper session management, and insufficient authentication mechanisms.
These vulnerabilities can expose user data, allowing attackers to steal information or access the app without proper authorization.
Recognizing these vulnerabilities helps developers proactively address them by implementing security best practices.
Best Practices for Secure App Code
We have already discussed how the first thing to do is always validate inputs to ensure the data being processed is what you expect, preventing injection attacks.
Additional software development best practices include the use of code obfuscation tools to make it harder for attackers to reverse-engineer your app's source code.
You should also avoid hardcoded credentials to enhance security. This means that you should never store sensitive information, such as passwords or API keys, directly in the source code.
Of course, we ensure that all of our developers here at Trio are familiar with these best practices and many more to ensure that their collaborative software development is a success.
What Security Measures Should Be Taken During App Development?
In our many years in the software outsourcing industry, we have seen how security should be integrated throughout the development process, with regular checks and tests to identify vulnerabilities before they become exploitable.
Security Testing for Mobile Apps
Security testing ensures that your app's defenses are strong enough to withstand attacks.
A comprehensive testing strategy includes static code analysis, dynamic testing, and vulnerability scans. These tests help developers identify potential weak points and areas of concern during development.
We highly recommend that you make use of automated security testing tools, but not rely on them solely, as there is also a lot of merit in manual security testing measures.
Penetration Testing as a Security Strategy
Penetration testing simulates real-world attacks on your app to identify vulnerabilities that could be exploited.
This type of testing mimics hacker tactics, allowing your developers to assess how resilient their app is against various threats.
Penetration testing should be conducted both before the app's launch and periodically post-launch in order to ensure mobile app security by addressing new concerns.
Implementing an App Security Checklist
A robust security checklist ensures that all key security practices have been implemented during development.
It also means that you can ensure that high-quality work is being done, regardless of whether the developer is working on security patches for you.
Your checklist should include ensuring secure API usage, encryption standards, and authentication methods.
Also, it should cover best practices such as session management, data protection, and backend security.

Discover Trio's Success Stories
See how Trio contributed to the growth of our partners and discover the potential of our team
How to Protect Your Mobile App from Security Threats?
Securing an app requires recognizing common security threats and implementing features that guard against any security concerns.
Often, many of these features need to be considered when you first design your app to ensure that they are addressed during the app development process.
Recognizing Common Security Risks
You can begin by conducting static code analysis to detect insecure data storage.
Tools like MobSF scan your code for any vulnerabilities, such as unencrypted sensitive data. This helps flag potential issues where data is stored in plaintext.
For authentication weaknesses, penetration testing is invaluable, as discussed above.
In terms of insecure communication, dynamic analysis tools like Wireshark monitor data exchanges between the app and server, ensuring data is encrypted during transmission.
This prevents risks like man-in-the-middle attacks by confirming the proper use of SSL/TLS.
Finally, ensure you're monitoring your third-party libraries with tools like Snyk. This helps identify outdated dependencies that might introduce security vulnerabilities, allowing you to keep your libraries secure and up-to-date.
These proactive steps help mitigate security risks before they become critical threats.
Security Features to Include in Your Mobile Application
To ensure mobile app security, developers should include several security features.
Multi-factor authentication is a great option to ensure that only authorized users can access the app.
Data encryption can also be used to enhance data security. This is done by securing sensitive data both in transit and at rest, of which we have already discussed its importance.
You can protect your app by using session timeouts to log users out after a period of inactivity, reducing the risk of unauthorized access.
What Are the Best Practices for Android App Security?
Android apps are often a primary target for attackers due to the platform's open-source nature. Implementing best practices is essential for securing Android apps.
Ensuring Security in Android App Development
Android app development requires careful management of app permissions and secure data storage.
Permissions should be restricted to the minimum required for the app's functionality, and sensitive data should be stored in Android's Keystore system, which provides hardware-based encryption.
Mobile Device Security Guidelines
Encouraging users to secure their devices by enabling two-factor authentication and ensuring regular software updates is crucial to enhancing app security.
Additionally, apps should detect jailbroken or rooted devices and limit their functionality, as these devices are especially vulnerable to attacks.
Security Tips for Android App Developers
Use ProGuard or similar tools to obfuscate code, making it more difficult for attackers to reverse-engineer the app.
Implement Device Fingerprinting to authenticate trusted devices and prevent unauthorized access.
How to Keep Your App Secure Post-Launch?
App security doesn't end once the app is launched. Post-launch monitoring and updates are essential to maintaining security as new threats emerge.

Monitoring Security Issues After Launch
Developers must implement monitoring systems to detect suspicious behavior after the app is released.
Setting up real-time alerts for anomalies, reviewing access logs, and regularly auditing app performance helps catch threats early.
You can add someone to your staff to help you do this; otherwise, building trust in tech partnerships and outsourcing this task through a company like Trio might be a good option for you.
App Store Security Guidelines for Developers
App stores like Google Play and Apple's App Store have strict security guidelines that developers must follow to ensure their apps are secure.
These guidelines include enforcing the use of HTTPS for data transmission, ensuring secure data storage, and incorporating user privacy policies.
Regular updates and maintaining compliance with these guidelines help protect users and maintain the app's reputation.
Mobile app security is a critical component of app development that protects both users and businesses.
By following these best practices—such as secure coding, regular testing, and continuous monitoring—developers can create robust apps that withstand the evolving landscape of cybersecurity threats.
Partnering with experts like Trio ensures that your app remains secure and reliable, giving users the peace of mind they deserve.
Whether you're developing for Android, iOS, or cross-platform, staying ahead of security trends is essential for success in today's competitive market.
Reach out to us to schedule a call and get started.
Frequently Asked Questions

Expertise
- JavaScript
- NGX
- HTML
- Node.js
- Vue.js
Subscribe to our newsletter
Related
Content
Continue Reading