Contents
Share this article
Key Takeaways
-
AI-powered fraud detection adapts where rule-based systems fail. It can analyze behavioral signals, device fingerprints, and transaction patterns in milliseconds, but the quality of the training data shapes everything.
-
Phishing attacks, smishing, and business email compromise (BEC) remain the most common entry points, and many of them now use generative AI.
-
Wire transfer fraud via BEC scams carries an average loss per incident far higher than card fraud, partly because instant payment settlement means the funds can’t be reversed.
-
Ransomware attacks against financial services have shifted from data encryption to double extortion, where attackers both encrypt systems and threaten to publish sensitive information.
-
Zero-trust architecture and multi-layered fraud defense address different parts of the same problem.
-
Cross-functional information sharing between cybersecurity, fraud, and AML teams produces measurably better outcomes.
Cybersecurity and fraud prevention have become two of the most difficult problems in financial services, and they are only getting worse.
Fraud detection used to mean spotting an unusual charge and calling the cardholder. Today, however, a scammer might impersonate a CFO over email, instruct a finance team member to wire hundreds of thousands of dollars to a new account, and be completely gone before anyone realizes what happened.
Cybercriminals craft phishing emails that bypass spam filters, leverage stolen credentials, and use synthetic identities built over months to pass KYC checks. The rise in embedded finance adds another layer of complexity onto all of this, as every third-party integration, every open API, and every new payment rail creates a potential attack vector that didn't exist before.
Let’s take a deeper look at cybersecurity and fraud prevention in the age of AI and real-time payments, including how to use AI for fraud detection, secure API integrations, apply zero-trust principles, and handle specific cybersecurity threats.
Our experts, whom we connect to companies through staff augmentation, carry real-world experience building and integrating fraud detection systems.
What Cybersecurity and Fraud Prevention Actually Covers in Fintech
AI fraud detection, in the banking and financial services industries specifically, refers to using machine learning models to analyze transactions and user behavior in real-time, apply behavioral analysis, and use predictive algorithms to identify fraud attempts and stop those transactions before settlement.
Traditional fraud prevention systems, on the other hand, rely on rule-based controls.
There is nothing wrong with these systems when they work, but they cannot adapt, which means that they leave financial institutions vulnerable when fraud tactics change. AI systems, by contrast, can adapt without manual intervention.
That adaptability matters because fraud patterns don't stay static.
Fraudsters evolve their methods specifically to stay below the thresholds of known detection rules. A rule written to flag transactions above $9,000 tells every criminal to stay below $9,000.
Cybersecurity and fraud prevention overlap more than organizational charts tend to reflect.
A phishing attack that steals credentials enables account takeover fraud. Malware installed through an unpatched vulnerability provides access to payment systems. Ransomware paralyzes operations.
These are cybersecurity incidents that directly cause financial fraud losses, and treating them as separate domains means the teams responsible for each often lack the shared actionable intelligence to respond effectively.
Common Fraud and Cyber Threats Targeting Fintech Companies
Understanding what you're defending against matters before choosing how to defend it. Here are the attack types that appear most frequently in fintech environments.
Phishing Attacks, Smishing, and Fraudulent Emails
Phishing is by far one of the most common entry points for financial cybercrime, and it has gotten significantly harder to identify.
A phishing email might appear to come from your cloud provider, a payment partner, or a regulator. The message asks you to click on a link, enter credentials, or share sensitive information. The link leads to a convincing spoofed page that captures whatever you enter.
Smishing works the same way over text messages.
A scammer sends what appears to be a fraud alert from your bank, prompting you to call a number or click on a link that delivers malware or harvests credentials.
Generative AI has made both significantly more dangerous since it’s removed tells like awkward phrasing, mismatched logos, and even generic greetings.
Instead, these attacks now use your name and role, and can even reference real recent events to appear credible.
For fintech teams building products, this matters both internally and for your end users.
How you design authentication flows, communicate with users about real alerts, and educate them about what you'll never ask for via email or text directly shapes how many fall for the imitation.
Business Email Compromise (BEC) and Wire Transfer Fraud
Business email compromise deserves its own category because the losses tend to dwarf those from card fraud.
In a BEC attack, cybercriminals either compromise or spoof a business email account, typically a CFO, a payment team lead, or a vendor contact, and use it to instruct a finance team member to authorize a wire transfer to an account they control.
With instant payment settlement, by the time anyone questions the instruction, these massive sums of money may already be irretrievable.
BEC attacks succeed because they exploit process gaps as well as technical issues.
A company with strong network security but no verbal verification requirement for wire transfer instructions remains wide open.
To prevent this, you need to require out-of-band verbal confirmation for any new or modified payment instructions, build call-back verification into the payment authorization process, and train your finance staff to treat even legitimate-looking email-only payment instructions as a vulnerability.
Related Reading: Web Service Security: 8 Ways to Secure Your Website
Identity Theft and Synthetic Identity Fraud
True identity theft involves using a real person's social security numbers, account credentials, or personal and financial information without their consent.
In this case, the victim usually discovers it through a credit alert or a fraudulent charge.
Synthetic identity fraud builds a fictitious person from a mix of real and fabricated data. A real social security number combined with a fabricated name and address creates an identity that passes basic KYC checks.
This one can lead to incredibly high losses since the synthetic person accumulates a credit history over months before the fraudster maxes out every available credit line and disappears.
We have seen this type of fraud growing a lot in financial services in recent years, partly because rule-based detection struggles with identities that have never triggered a fraud flag before.
Advanced Persistent Threats (APTs) and Ransomware
APTs represent a different category of cybersecurity threat where someone gains access and then maintains a presence in your systems for weeks or months, moves laterally until they reach high-value targets.
Ransomware attacks are a good example of this.
Modern ransomware uses a double extortion model where they encrypt the target's systems to paralyze operations, and then threaten to publish or disseminate sensitive information unless a ransom is paid.
To recover your own software, you’ll probably need both technical response and legal counsel.
As a fintech firm, the biggest detriment you will face here will not be financial loss but instead the reputational implications of customer data becoming public.
Unpatched systems are a common initial access vector. A known vulnerability in an unpatched version of a widely used library can give an adversary a foothold regardless of how well everything else is secured.
API and Embedded Finance Attacks
Using third-party apps to handle a specific service has become very normal in fintech. If you don't have a banking license, run your transactions through a payment service provider that does.
The issue comes from needing to control how third-party interfaces interact with your platform without opening new vulnerabilities.
Cybercriminals often target API integrations specifically, looking for real-time transaction spikes, malformed payloads, and unauthorized access patterns.
A poorly secured embedded finance integration can give an attacker access to your payment stack through a vendor's systems rather than your own, which means your internal controls don't protect you.
AI can monitor anomalous API behavior and flag these patterns before they escalate, but only if security monitoring covers third-party API traffic alongside internal systems.
How AI Powers Fraud Detection in Financial Services
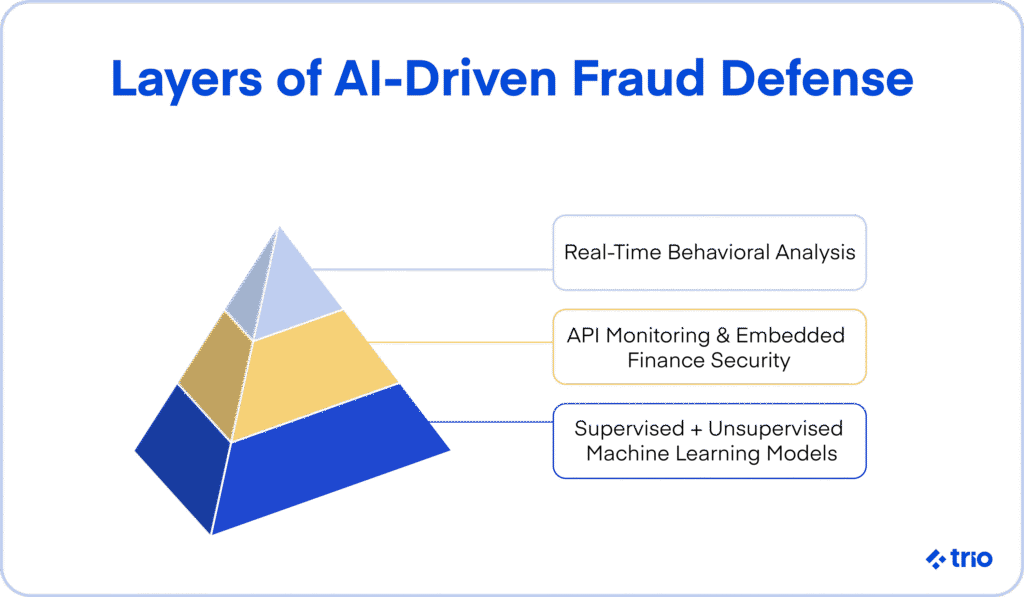
The most effective AI fraud detection systems take a layered approach, allowing them to keep learning, analyze behavior, and protect areas with particularly high fraud risk.
Supervised vs. Unsupervised Learning
Supervised learning involves a person putting together a structured, labeled dataset used for effective training.
This learning helps AI fraud detection solutions identify and prevent fraud patterns we already know about, such as known card fraud signatures or previously documented phishing indicators.
Unsupervised learning happens when your AI model trains on real data with no labeling, so the model can identify patterns that may indicate fraud without a human having pre-defined what those patterns look like.
This is the kind of learning that can happen in real time, which makes it an essential practice because fraudsters actively change their methods to evade known rules. Unsupervised models catch the novel approaches.
Real-Time Behavioral Analysis
Many accurate models analyze user behavior, device fingerprints, and access patterns together.
For example, this might include something like a user logging in from a location they've never used before and immediately initiating a large transfer to a new payee.
This behavior probably doesn’t trigger any individual rule, but the combination of signals suggests a much higher fraud risk.
We’ve seen this being incredibly effective in preventing account takeover and card fraud.
AI for Embedded Finance and API Security
AI can monitor anomalous API behavior and look for real-time transaction spikes, malformed payloads, and attack vectors that appear only at the API layer.
Without AI monitoring, you are only really able to see these attacks in post-incident analysis, by which point the fraudulent activity has already cleared.
AI-Powered Threat Intelligence and Generative AI
We have already briefly mentioned that generative AI (GenAI) now works on both sides of the fraud problem.
On the attack side, fraudsters use it to generate realistic phishing emails, create more complete synthetic identities, and craft social engineering scripts that sound like real customer service interactions.
On the defense side, AI-powered threat intelligence can run fraud simulations, generate synthetic training data to improve detection models, and help security teams identify new fraud patterns faster than manual analysis allows.
You need to be careful, though. When using AI in fraud detection, you still need human oversight.
Models trained on historical fraud data may not catch novel cyber-enabled fraud patterns until they've appeared enough times to register statistically.
Key Benefits of AI-Powered Fraud Prevention for Fintech CTOs
There are a couple of benefits that stand out above others, and are critical for fintech CTOs to consider.
- Real-Time Fraud Detection: Faster detection means fewer irreversible losses, particularly in instant payment environments. AI can detect fraud in real-time, analyzing thousands of data points in milliseconds, making it viable for instant settlement.
- Fewer False Positives: With every false positive, a legitimate customer can't make a payment, and depending on your response protocol, they may not regain access to those funds for days.
- Scalability: AI grows with your transaction volume. There is no delay like there would be when you need to look for a person to deal with a sudden, rapid increase in transactions. You also pay for only what you need.
- Customer Trust: Customer trust shapes retention, and in fintech, where comparable alternatives usually exist, you can't afford to give customers reasons to question your competence.
- Regulatory Alignment: Regulations like PCI DSS, SOC 2, and GDPR serve to protect clients and reduce fraud. AI agents can support regulatory compliance by automating audit trails, monitoring for policy deviations, and alerting teams.
Challenges of Implementing AI-Powered Financial Cybersecurity and Fraud Detection
Data quality and bias are the biggest issues, alongside compliance and explainability.
Your AI model makes decisions based on the data it trains on. Poor data quality or unbalanced datasets tend to produce systems that flag certain behaviors or user profiles disproportionately while missing others entirely.
Making sure your model trains on a diverse, audited dataset isn't just a technical requirement. In regulated environments, biased fraud detection can create legal exposure alongside operational risk.
Regulators also demand transparency. The issue comes from how difficult it sometimes is to walk through how AI reached its decision.
Explainable AI (XAI) has become increasingly important as financial institutions use it to make decisions that affect customers.
A Multi-Layered Fraud Prevention Strategy for Fintech
Your fraud prevention strategy needs to fit your specific environment, since there are too many factors at play for a generic option to be as effective as you need it to be. Here are the layers that tend to matter most.
Actionable Intelligence: Connecting Cybersecurity, Fraud, and AML Teams
One of the most consistently cited gaps in financial institution fraud prevention involves intelligence that sits siloed in different teams.
The FS-ISAC Cyber Fraud Prevention Framework documents how financial institutions that coordinate across cybersecurity, fraud, financial crimes, and AML functions using shared, actionable intelligence see dramatically better outcomes than those working individually.
Adopt Zero-Trust Architecture
Security improves when you assume no user or system deserves automatic trust, regardless of whether they came from inside or outside the network.
Zero-trust architecture means implementing microsegmentation, continuous verification, and role-based access controls that require authentication at every step.
AI behavioral analysis feeds naturally into this model, flagging when a verified user starts behaving differently from their established pattern.
Password policies form one of the most commonly neglected zero-trust controls. Enforcing strong password requirements, mandating multi-factor authentication, and monitoring for unauthorized access attempts cost relatively little compared to the breach they prevent.
Protect Against Ransomware and Malware
Ransomware attacks paralyze operations. The best defense involves reducing the initial access opportunities they depend on.
Unpatched systems represent the most common entry point. A regular patching cadence, even just keeping critical systems current, removes a significant proportion of the attack surface that ransomware exploits.
Endpoint protection, network segmentation, and immutable backup systems that stay isolated from production environments make a ransomware attack recoverable rather than catastrophic. Without offline backups, the choice often comes down to paying the ransom or rebuilding from scratch.
Incident response planning matters here, too.
Teams that know exactly what steps to follow when ransomware hits, including when to contact your bank, when to engage legal counsel, and which federal agency to notify, contain losses more effectively than those that figure it out under pressure.
Secure Your Embedded Finance Stack
APIs and embedded finance integrations represent some of the broadest attack vectors in modern fintech cybersecurity.
OAuth 2.0, mutual TLS, and AI-powered anomaly detection all help, but every single integration needs its own scrutiny, not just the highest-profile ones.
A low-traffic internal API that passes payment credentials through an unvalidated third-party middleware can create exposure that your customer-facing security controls don't cover.
Continuous monitoring of third-party usage keeps your overall risk picture current as vendors update their own systems.
Simulate Attacks and Build Incident Response Plans
Simulating attacks realistically and regularly helps you find vulnerabilities before cybercriminals do.
The results of these simulations feed into incident reports that give developers actionable fixes and provide documentation for compliance audits.
A response plan that assigns clear ownership, specifies communication protocols for internal stakeholders and affected customers, and includes contact details for your bank, legal counsel, and relevant federal agencies helps significantly when an actual incident hits.
Final Thoughts
The strategy above only works if your team has the expertise to execute it.
You need skilled developers who understand both the technical and regulatory dimensions of fintech cybersecurity, not just engineers who can write detection rules.
At Trio, our developers bring experience in fintech-specific security and compliance and have built and integrated AI-powered fraud detection systems for other clients.
If you're evaluating your fraud prevention strategy or want to add a fintech cybersecurity specialist to your team, reach out for a security-ready consult.
Frequently Asked Questions
Actionable intelligence refers to fraud and cyber threat data that gets shared across cybersecurity, fraud, and AML teams in a format that directly informs detection rules and response protocols.
Ransomware attacks affect fintech companies by encrypting critical systems to paralyze operations and increasingly threaten to publish sensitive customer data unless a ransom is paid. Prevention relies on regular patching, network segmentation, and offline backups.
Zero-trust architecture in cybersecurity treats every access request as potentially unauthorized, requiring continuous authentication and verification regardless of whether the request originates inside or outside the network.
Phishing emails and smishing text messages impersonate banks, payment providers, or regulators and ask recipients to click on a link, share sensitive information, or enter credentials. Generative AI has made fraudulent emails significantly more convincing.
The most common cybersecurity threats facing fintech companies include phishing attacks and smishing targeting staff and customers, business email compromise, synthetic identity fraud, ransomware attacks, API vulnerabilities in embedded finance stacks, and advanced persistent threats targeting payment infrastructure.
Business email compromise fraud involves cybercriminals either compromising or spoofing a business email account to instruct finance staff to authorize fraudulent wire transfers.
AI fraud detection in banking and financial services covers the use of machine learning models to analyze transactions and user behavior in real time, identify fraudulent patterns, and stop fraud before it executes.

Expertise
- JavaScript
- NGX
- HTML
- Node.js
- Vue.js
Subscribe to our newsletter
Related
Content
Continue Reading